In this post, I wanted to highlight the key benefits of using Generation 2 virtual machines in Azure. These have been in general availability for a while now but from my own experience I don’t see too many Gen2 virtual machine deployments in the wild yet.
If you have a Hyper-V background like myself, then you will already know that Generation 2 Hyper-V virtual machines have UEFI support instead of a legacy BIOS boot process. The other main difference is that Generation 1 virtual machines can boot from IDE disk controllers where as Generation 2 virtual machines boot from SCSI disk controllers. Therefore, choosing which Generation type to use was usually based on the hardware that you had available.
With Azure, hardware isn’t a concern for us as this is supplied by Microsoft so choosing the Generation for your virtual machine should be based on features and support.
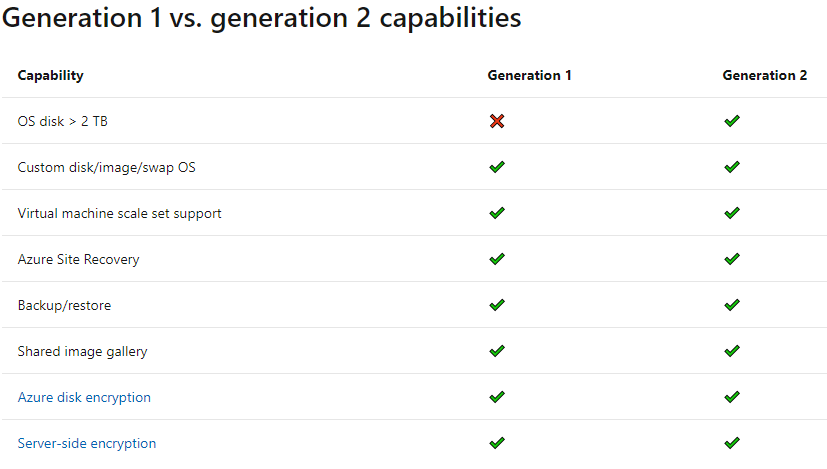
Thankfully, at this point in time there is feature parity for most things. Generation 2 virtual machines are not yet available for all virtual machine sizes or operating systems but most of the common types are supported now with the notable exception of A-series VMs.
Unfortunately Azure still does not support VHDX files for disks so if you are uploading your own disks then they need to be in VHD format even for Generation 2 virtual machines. The Generation type must be chosen at the time of the VM creation, there is no option to convert later. From a pricing perspective, there is no difference to the cost between Gen1 and Gen2 virtual machines in Azure.
So, what difference does it make?
There are a few fringe benefits such as slightly better boot times and increased OS disk size support but the real reason here is security.
I need to caveat this here and point out that the below feature is currently in preview which means it is not production ready yet. This does not mean that you should not choose to create Generation 2 virtual machines as this will be a pre-requisite requirement and remember this needs to be set at the time of virtual machine creation.
The feature I am talking about which is really the highlight of this article is called ‘Trusted Launch‘ which is effectively the Azure equivalent of Secure boot and vTPM on Hyper-V.
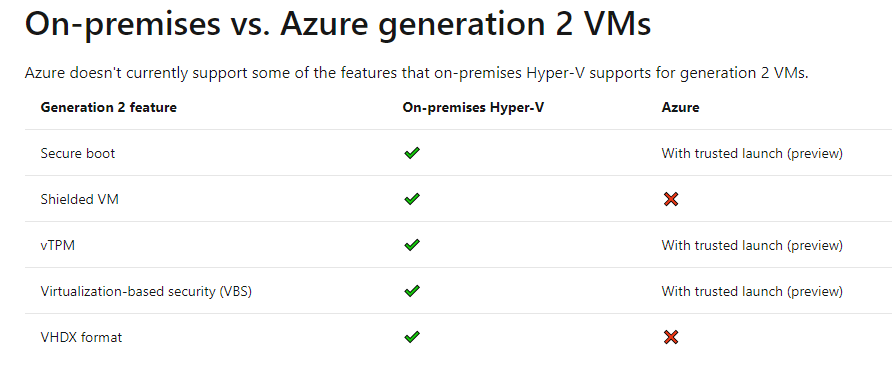
Please be aware that this preview feature has quite limited support currently and most importantly does not yet support Azure Backup or Azure Site Recovery however I really believe this is one to keep a close eye on due to the additional integrity protection it offers.
Trusted Launch (Preview)
When Azure CTO Mark Russinovich is the one to announce the public preview, you know it’s something important. Trusted launch offers additional layers of security to your virtual machines, helping to protect them from rootkit malware attacks against the virtual machine’s firmware, drivers, OS kernel and bootloader. These are attack vectors that your bog standard anti-virus software simply can’t fully protect from within the operating system.
Trusted launch has integration with Azure Security Center for monitoring and assessment purposes allowing you to monitor these additional services centrally along with the existing security services that Azure Defender offers.
There will be no additional cost for Trusted launch and for me once it goes into general availability and offers Azure Backup support this should be a “no brainer” for most customers. When it comes to security you always want to add as many layers of protection as you can and usually it’s only when costs start to make it prohibitive that customers tend to decide that they have enough security already in place.
If you want to try it out now, then Trusted Launch needs to be enabled when deploying your virtual machines but it will be possible to convert existing Generation 2 virtual machines once Trusted Launch reaches general availability.
You can find steps on how to deploy Trusted Launch here: Preview: Deploy a trusted launch VM – Azure Virtual Machines | Microsoft Docs
