Welcome to the final part of my well-tempered Azure tenant series for MSPs. This time we will take a look at Microsoft Defender for Cloud. This service has undergone some recent name changes having been formerly known as Azure Security Center (Standard tier) and then simply Azure Defender before taking its current name. It is now part of the larger Microsoft Defender family of products but the purpose of Microsoft Defender for Cloud is to improve your overall Azure cloud, hybrid and now even your AWS and GCP security posture by providing additional security tools and management capabilities.
Part 7: Microsoft Defender for Cloud
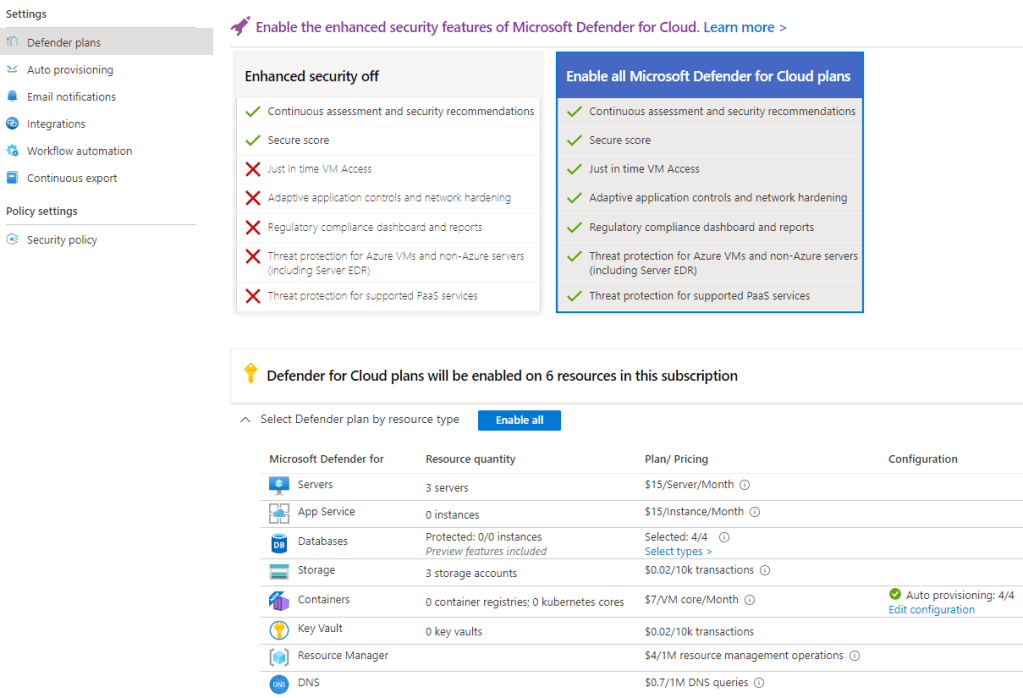
Microsoft Defender for Cloud is not a single product, rather a collection of different security plans that can be enabled for the different Azure services that you want to protect. Each plan has its own pricing model and can be enabled per Azure subscription.
At the time of writing this post the following plans are currently available:
- Microsoft Defender for servers
- Microsoft Defender for Storage
- Microsoft Defender for SQL
- Microsoft Defender for Containers
- Microsoft Defender for App Service
- Microsoft Defender for Key Vault
- Microsoft Defender for Resource Manager
- Microsoft Defender for DNS
- Microsoft Defender for open-source relational databases
- Microsoft Defender for Azure Cosmos DB (Preview)
There is also a separate product available called Microsoft Defender for IoT which has a fixed monthly or annual commitment pricing model per 100 devices monitored.
It’s worth noting that you can enable these paid plans for free for a 30 day period (with some limitations).
I won’t go through all of the various features of Microsoft Defender for Cloud in this post but I do want to cover the initial set up and how we can use this service to protect our Azure and hybrid resources.
Setting up
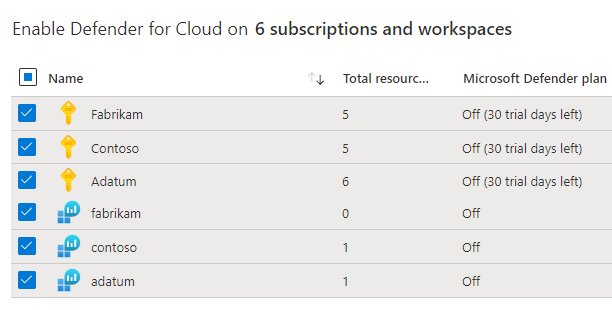
As mentioned, Microsoft Defender for Cloud must be enabled on the subscription level but you can enable (or “upgrade”) the service for multiple customer subscriptions at once. If you only want to enable this for resources that are monitored by your Log Analytics workspaces then you can select these workspaces only. However, this is limited to Microsoft Defender for servers and SQL server on machines protection only.
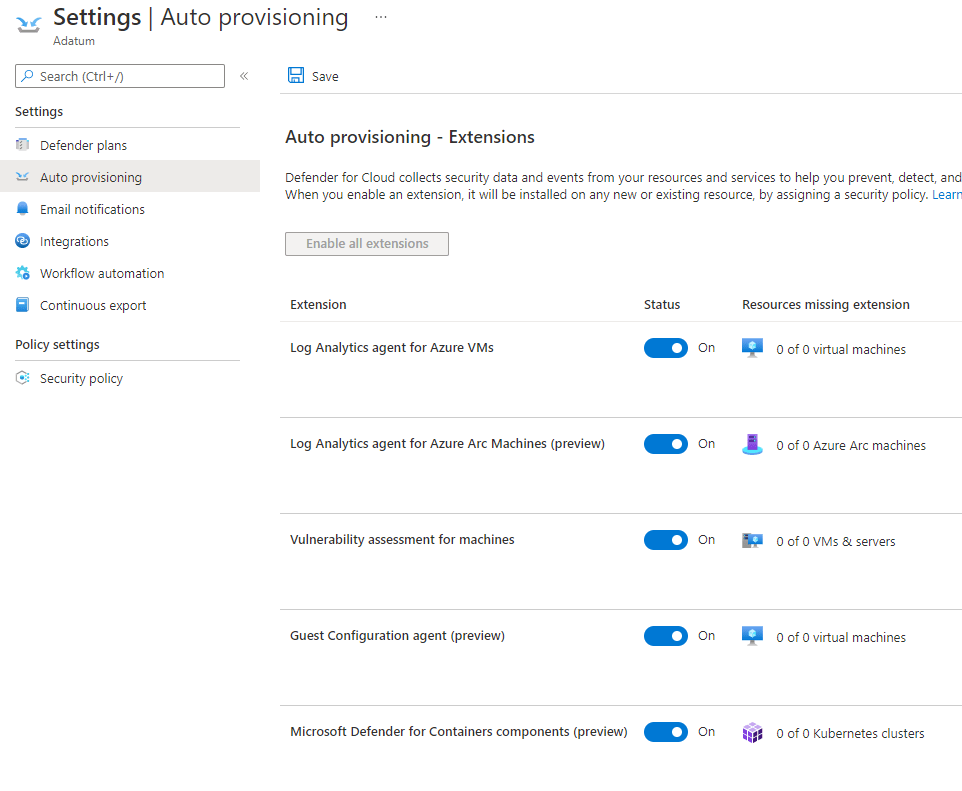
Once the service is enabled you should get a prompt to install agents automatically to any virtual machines that you have deployed. This can be done now or at a later stage if you want to use the Microsoft Defender for servers plan.
With the service upgraded, it will automatically commence the free 30 day trial period and you will find that you must manage each Azure subscription’s environment settings separately. By default, all of the available plans will be enabled so you may want to disable some of these plans if you do not intend to use them in order to avoid unexpected costs.
I recommend to go through each of the environment settings options but in particular I would consider enabling auto provisioning so that any future VMs or containers are protected automatically. This will require a Log Analytics workspace and we can use the same workspace that we have referenced in previous posts in this series.
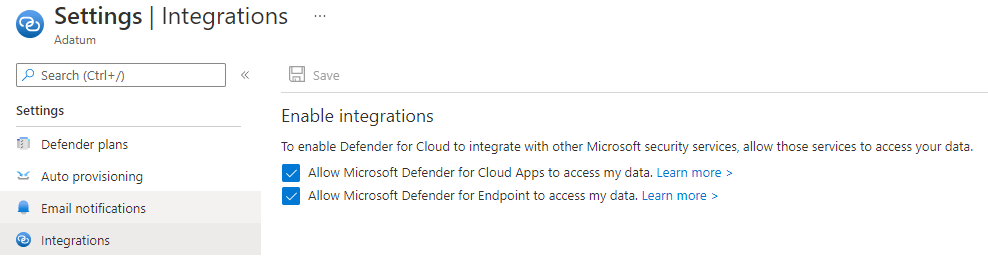
I also recommend that you leave the integrations enabled, this will be useful for integrated reporting purposes later on.
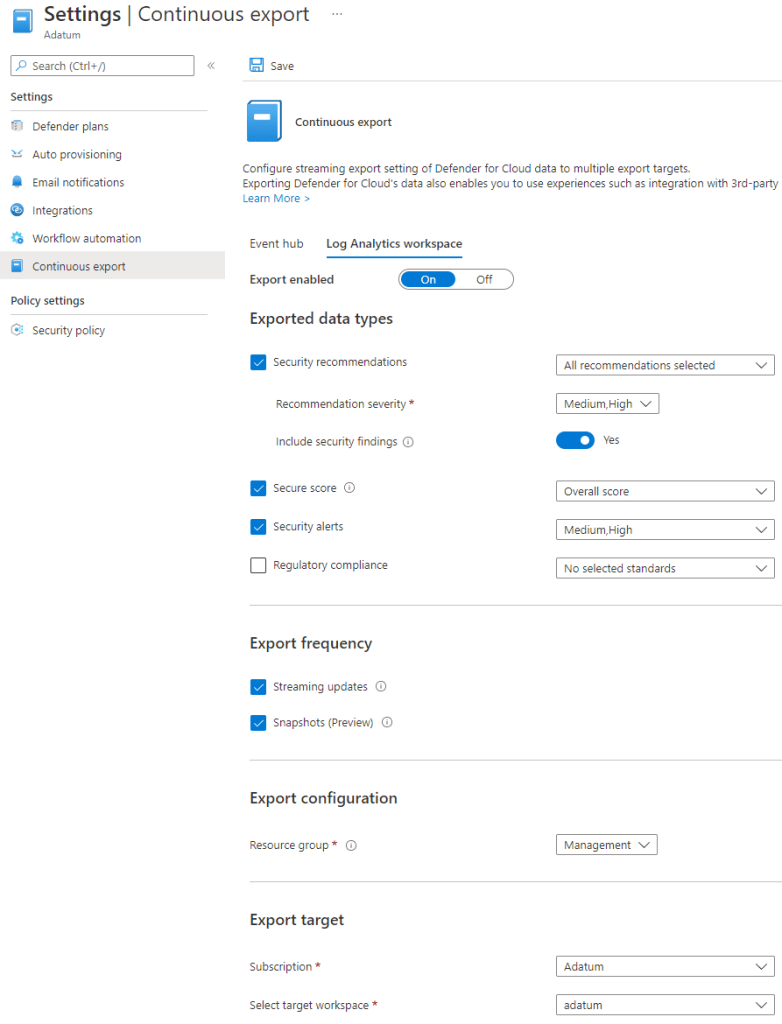
You may want to also configure a continuous export of your customer’s security score and alerts to their Log Analytics workspace. This will be useful later when comparing your overall customer security postures against each other. You can also choose to create alert rules to trigger alerts based on data that is exported to your workspace.
The below continuous export settings are what I recommend using as otherwise with additional log data ingestion you may incur much larger Log Analytics costs.
You can also assign compliance policy initiatives, set up alert email notifications and configure automated workflow responses to security alerts and recommendations using Logic Apps in these environment settings.
Now, we wait…
Focussing on Microsoft Defender for servers here, we will have to wait a little while before the security telemetry starts to appear from the deployed guest OS agents but after some time has passed the best place to start looking is with the recommendations page.
These recommendations can be filtered across all of your customer subscriptions giving you a unified view of security risks and recommendations across your entire customer base.
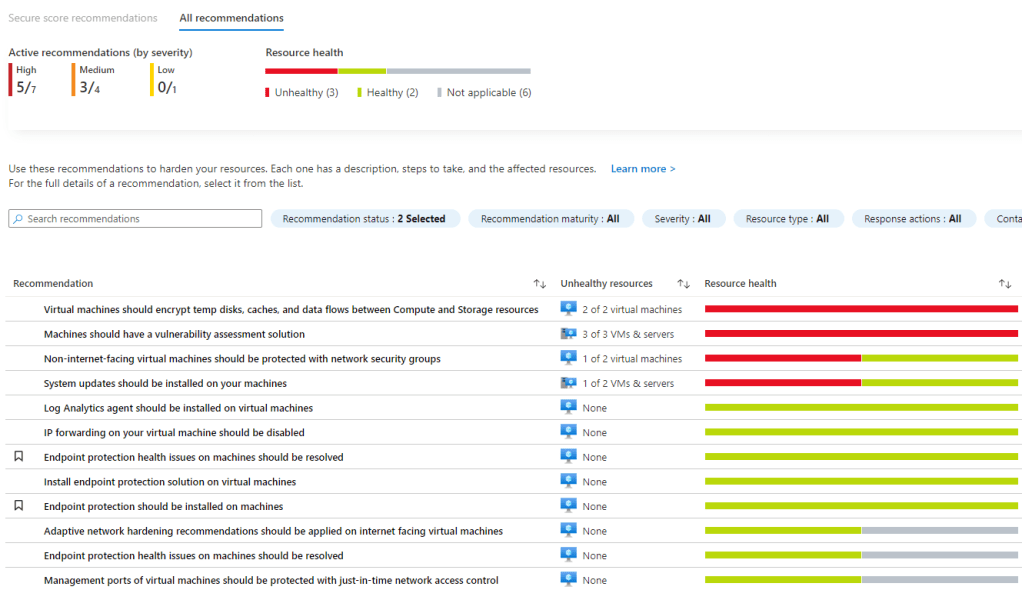
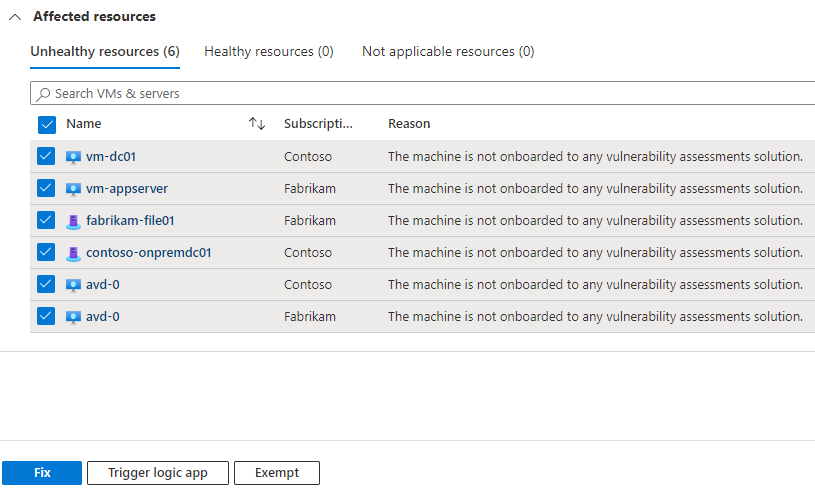
Some of these recommendations can be remedied via a ‘quick fix’ option which again can be done across tenants and subscriptions at once. You will note below that this also includes any non-Azure virtual machines that are managed using Azure Arc, we covered this in the previous post of this series. If you are using the AWS or GCP connectors (currently in preview) then you will see any security recommendations from connected virtual machines on these cloud platforms here also.
Similar to Azure Monitor, we will find some useful workbooks here but with more of an emphasis on security.
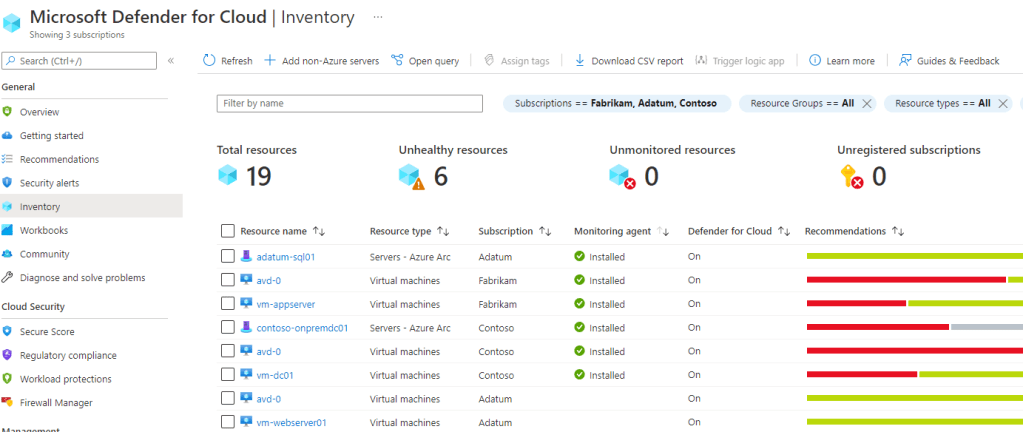
The below is an inventory report showing all of my Azure (and Azure Arc) resources that can be protected by Microsoft Defender for Cloud and their current protection and recommendations status.
Below is a secure score report based on a continuous export to Log Analytics. This workbook allows you to easily compare the overall security posture of your customers to one another and track this as a trend over a time period.

Microsoft Defender for Endpoint
Microsoft Defender for Cloud includes an integrated license for Microsoft Defender for Endpoint which can be used for Azure Windows and Linux servers as well as Azure Arc managed servers. Azure Virtual Desktop Windows client machines are also supported.
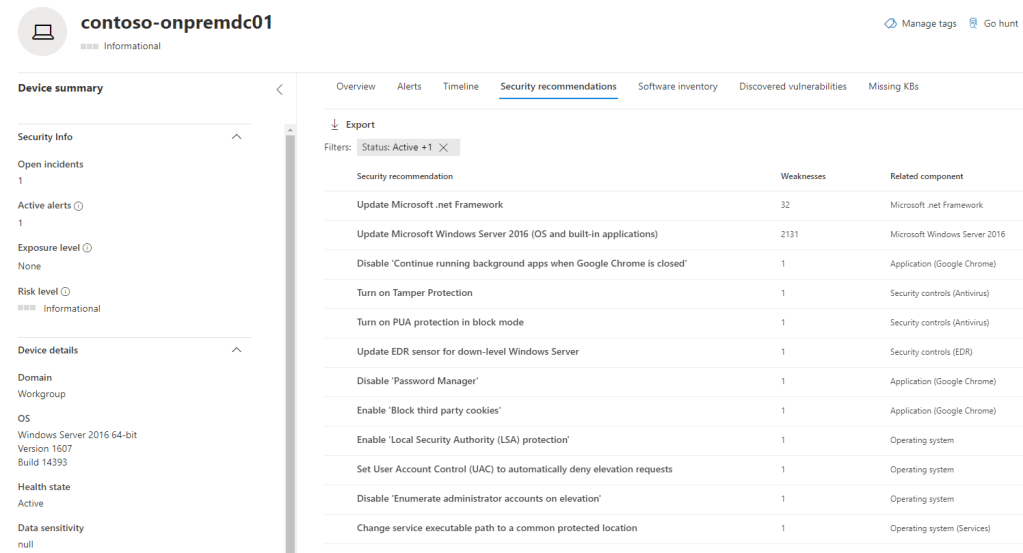
You can track your device inventory and alerts as well as review security and vulnerability assessments in the Azure portal but this information is also in the customer’s Microsoft 365 Defender portal.
This is great because you now have a unified management portal for security if you are using any of the other Microsoft Defender products for your customers.
…and that’s a wrap
This concludes my series on well-tempered Azure tenants for MSPs. The idea of this series was to give an insight into some of the management and monitoring capabilities that can be used across multiple customer Azure tenants for managed service providers. This is the true value added service that an MSP can provide for their customers and it really is up to you to decide just how far you want to take your managed service offering.
There are a great set of tools now available for helping with this and it is getting better all the time. In closing, I hope this blog series has given a helpful flavour for some ideas that you can use for your own MSP service offering.
Please feel free to reach out to me if you have any questions or want to discuss any concepts or ideas around this.

One thought on “MSP: The well-tempered Azure tenant – Part 7”