The issue
With more and more services going cloud native it’s becoming increasingly more common for organisations not to rely on DNS servers anymore. Just like how we are seeing new ‘greenfield’ organisations going fully cloud native and opting not to use domain controllers at all. We are also starting to see organisations not want to provision a server based DNS service.
In the past, whenever we used an Azure Point-to-Site VPN connection you needed to use a DNS forwarder or conditional forwarder to resolve private DNS names in Azure. This meant more infrastructure, more maintenance, more potential DNS issues because of course “It’s always DNS”.
Nowadays we have many people working remotely who may need to access some Azure hosted resources but how to manage DNS resolution over a Point-to-Site VPN connection?
There’s a new kid in town
Thankfully we have a new service in Azure which is in public preview at the time of writing – Azure DNS Private Resolver. It’s purpose is quite simply to allow you to query private DNS zones in Azure from on premises and vice versa without requiring any server based DNS services.
Procedure
1. Create Private DNS Zone
So let’s start with a private DNS zone. I have no DNS server in my Azure environment and I don’t want one either! Therefore, I have created a private DNS zone called alanco.com for my organisation and I have linked this to my virtual network with auto registration enabled.
As you can see, I have three hosts registered in my private DNS zone currently.

2. Create Azure DNS Private Resolver
Now we create our Azure DNS Private Resolver service. This service comes with two configuration options which can both be used together if required.
Inbound endpoints and outbound endpoints.
In a nutshell, inbound endpoints are used to resolve incoming DNS queries entering an Azure virtual network externally such as from on premises and an outbound endpoint is used as a conditional forwarder on outbound DNS queries outside of Azure such as to on premises.
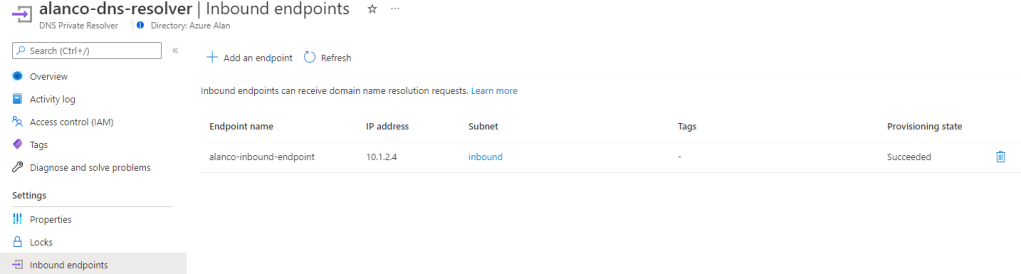
In this scenario, we will be creating an inbound endpoint as we will have incoming traffic (DNS queries) from our VPN clients who are connecting in externally. This endpoint should be deployed to its own subnet and an IP address will be assigned automatically from that subnet range.
On the client side, when you download the Azure VPN client from the Point-to-Site configuration screen of your virtual network gateway, you also receive a VPN configuration file entitled ‘azurevpnconfig.xml‘. This file must be modified to add your desired DNS server IP address and this is where our Azure DNS Private Resolver comes in.
3. Modify the VPN config file
We need to set the DNS server to the IP address of the inbound endpoint of the Azure DNS Private Resolver.
Optionally, you can also set a DNS suffix addresses in the config file, this will prevent having to specify a fully qualified domain name for the hosts in your DNS zone.
Below is a snippet taken from my VPN config file. Note, the settings I just mentioned must be entered between the <clientconfig> tags.
<clientconfig>
<dnsservers>
<dnsserver>10.1.2.4</dnsserver>
</dnsservers>
<dnssuffixes>
<dnssuffix>.alanco.com</dnssuffix>
</dnssuffixes>
</clientconfig>
4. Import the VPN connection profile and test
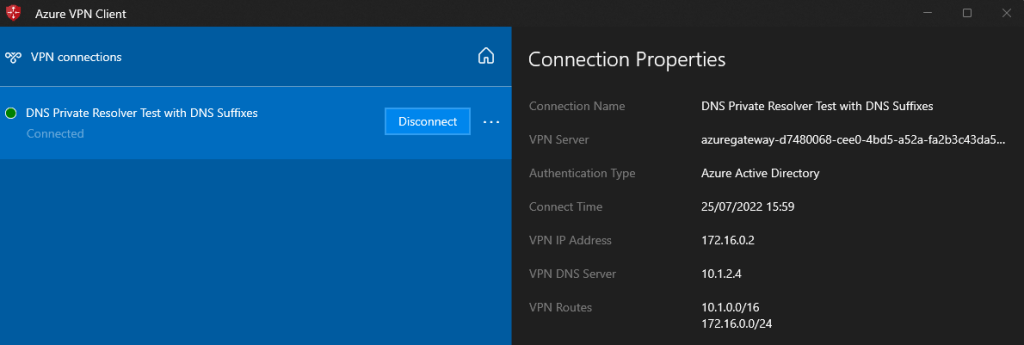
Once you have saved your config changes you can then import the configuration into the Azure VPN client. This step must always be done after making any changes to the VPN configuration.
Here we can see that my Azure VPN client is connected with my customised configuration profile. Note the DNS server IP address is set to the inbound endpoint of my Azure DNS Private Resolver.
Now that we are connected via the VPN we can test that our DNS resolution is working.

Conclusion
A very simple service to deploy and configure and it integrates pretty seamlessly from my experience. The trade off on this one for me is the price. Clocking in at over €171 per month for my region, this would be considerably more expensive than a low end Virtual Machine acting as a DNS server or DNS forwarder.
However, it’s always good to have a PaaS alternative to an age old infrastructure service.

Thanks for the post. It’s annoying that the DNS can’t be set with DHCP when the user connects and gets their IP address. I wonder why they do that?
LikeLike