There has been a recent Azure portal UI update to the networking features of the Azure App Service. This is accessed through the Networking option under the Settings section and as you can see below it presents the user with a nice overview of which networking services have been enabled as well as a centralised overview page to see your inbound and outbound public IP addresses as well as your configured domains.

In addition to this I really like the quick links into getting both an Azure CDN and Azure Front Door service quickly provisioned and automatically configured from this page also.
This blog will go through what each of these networking services can be used for at a high level so that you are aware of the current networking capabilities for controlling inbound and outbound traffic to and from your Azure App Service.
This blog will focus on the multitenant App Service plans only. If you need full networking control then you can deploy an App Service Environment (ASE) which is a single tenant service that is deployed directly to your virtual network.
Note: The availability of some of these features will vary depending on which type of App Service Plan you are using but I will outline the requirements for each below.
Access Restrictions (Available on all plans)
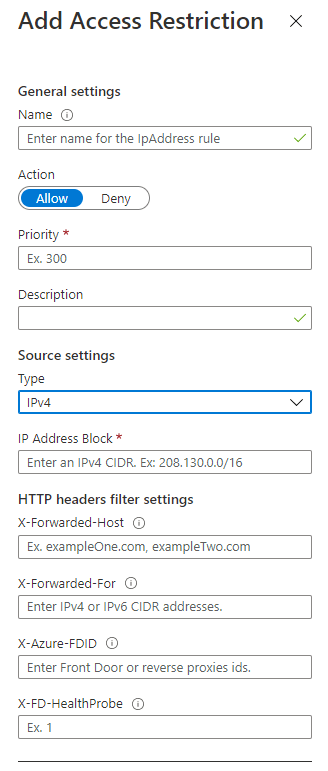
This one is straightforward enough, it’s a basic inbound allow/deny ruleset for your applications. You can configure this setting for each individual application on your App Service Plan and even have a different set of restrictions for the Kudu service if desired.
Access can be restricted to IPv4/IPv6 address or CIDR ranges and also to virtual networks and service tags. Multiple rules can be added and will be evaluated in order of priority.
There are even some options to restrict traffic based on HTTP headers but this is limited to the options in the image shown below.
App Assigned Address (Standard, Premium and Isolated plans)
This a feature for where you may want to assign a dedicated public IP address to your application. Remember, Azure App Service is multi-tenanted so it will have a shared public IP address by default. If a dedicated public IP address is required, for example for IP-based SSL as shown below then you can enable this feature but note that you only get one IP-Based SSL connection included in the cost of your App Service Plan, additional connections come with increased costs.
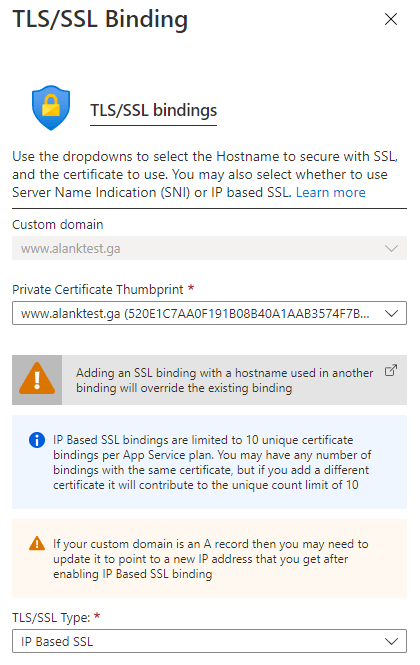
Configuring IP-Based SSL will change your inbound public IP address so remember to update any public DNS records if required.

Private Endpoints (Premium v2 and v3 plans only)
Private endpoint is a service that allows you to create a network interface resource and attach your application to a virtual network. This will provide your application with a private IP address for inbound traffic. Most commonly this feature would be used to host an application internally within your organisation and where you don’t want it to be accessed publicly over the Internet.
Another example might be if you were protecting your application with a virtual network based WAF, this way you would not need to expose the public endpoint of the App Service.
Private endpoints do carry an additional cost, this is a per hour cost for the service and also an additional per gigabyte cost based on inbound/outbound data processed by the private endpoint.

VNET Integration (Standard, Premium and Isolated plans)
VNET integration allows you to integrate your multi-tenanted application with a virtual network for outbound traffic. Therefore you can use this feature for outbound access from your application to your virtual network resources or any resources connected to the virtual network via VNET peering or through VPN connections. This feature cannot be used for private inbound connections however, in this case you would combine it with private endpoints as mentioned earlier.

Hybrid Connections (Basic, Standard, Premium and Isolated plans)
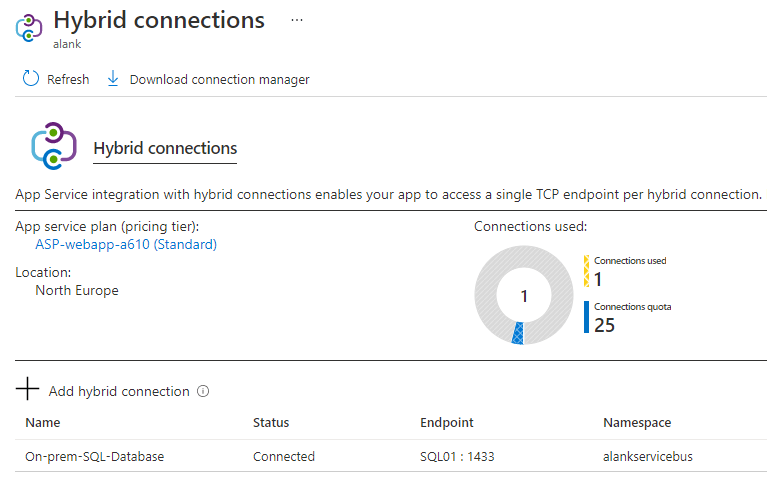
Hybrid connections are useful where you need to make outbound calls to external endpoints that are not otherwise connected to your application. This service utilises the Azure Relay connection service to send outbound traffic from your application over TCP port 443. Traffic is encrypted using TLS 1.2 and sent over the Internet to where you have the hybrid connection manager agent installed. Your application can simply make a DNS request to the connected endpoint which relays the TCP traffic through the hybrid connection.
The hybrid connection manager needs to be installed on a device running Windows Server 2012 or later and must have access to Azure over TCP port 443. Generally this therefore does not require any additional firewall ports to be opened.
The actual endpoint that you need to connect to just needs to be able to communicate with the device where the hybrid connection manager is installed, it doesn’t even need to have direct Internet access.
You can have multiple hybrid connections per application with an upper limit on the total number of connections per App Service Plan depending on the tier of the plan that you are using.
In Conclusion
To sum up, it’s quite common to use a combination of several of these networking features depending on the solution that you are providing and although it may not be strictly required, you can greatly enhance the security of your application by utilising some of the features covered in this post.
