Welcome to part 3 of my well-tempered Azure tenant series for MSPs. At this point we have already covered how to onboard your customers for delegated management using Azure Lighthouse. Now it is time for us to start making use of that delegated access and to start managing our customers.
This post will focus on a core service that I think most MSPs will likely be using and perhaps struggling to manage at scale – Azure Backup. Fortunately for us, this service has some nice reporting features that benefit from Azure Lighthouse and can be used at scale across customer tenants.
Part 3: Azure Backup
I will make the assumption that your customers have a number of Azure Backup services in place already rather than covering how to set this up here. This might be a combination of backup for native Azure resources such as Azure virtual machines and Azure Files buts also on-premises backups using MARS, MABS or DPM. Either way, you will want a consolidated report that can show you the status of everything in one place. There are a few different reporting features available through the Azure portal and I will go through these here.
Backup Explorer
Let’s start with Azure Backup Explorer. This service does not require any additional setup to be able to view backups across your customer tenants once you have Azure Lighthouse in place, however this service is limited to Azure virtual machine backups only.
Therefore if you are only backing up Azure VMs and need to just get some report data at a glance this service can be a quick way to access what you need. This service is accessed through any one of your delegated recovery services vaults, just click on the hyperlink for Backup Explorer on the overview pane and you can filter the report on anything up to 1,000 subscriptions across multiple tenants.

Backup Reports
A more comprehensive tool that we can use is Backup Reports. This solution offers support for most Azure Backup services today including the on-premises backup solutions MARS, MABS and DPM so it will allow you to consolidate reporting for your on-premises backups along with your Azure based resources.
This service is based on diagnostic log ingestion into Log Analytics so you will need to configure this for each recovery services vault for every customer. Fortunately there is an Azure policy available to set this up as a remediation task and we will cover how to do this in the next post in this series.
For now, the manual deployment steps for this can be found here. I recommend to use a separate Log Analytics workspace per customer. This has a number of advantages over using a single shared workspace such as providing each individual customer with ownership and access control of their data and also split billing so that each customer’s Log Analytics costs can easily be associated with their own Azure subscription. I recommend to create a ‘management’ resource group on each of your customer tenants. This can then be used for any customer level management resources that need to live on the customer’s own tenant.
Once the workspaces are created and the recovery service vault diagnostics are sent to the workspace you should wait 24 hours for your first backup data to be ingested fully. At this point you can select multiple workspaces (up to 100 currently) in the backup report and consolidate the data from these workspaces into a single report view.


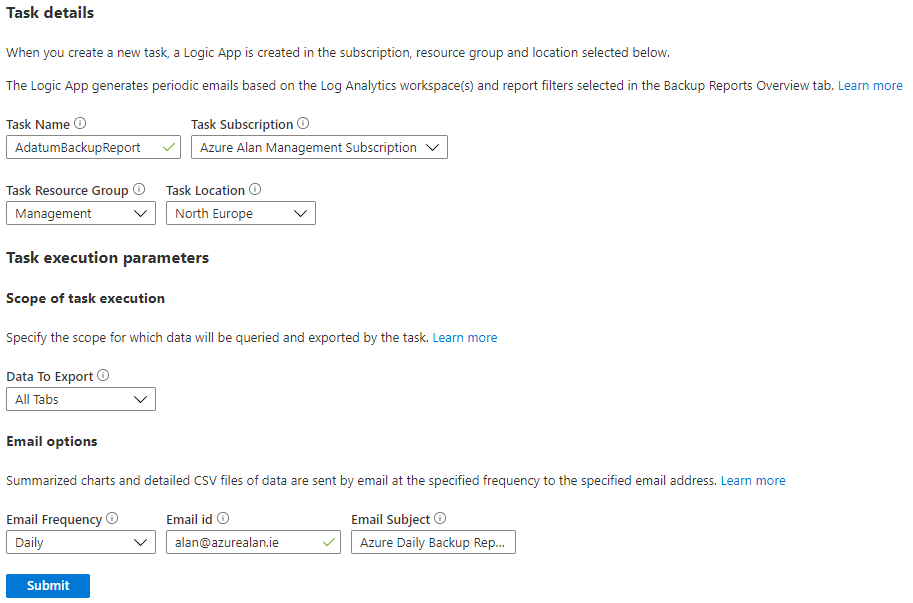
For those of you who still like to have a daily backup report emailed to you there is a feature for this here also. Enabling this feature will create a Logic App and some API connections. This should be deployed to your management tenant as it can then report on all of your delegated customer backups. Just remember to go into the API connections of the Logic App and authorise the API connections once the deployment has completed after you submit the task execution below.
Backup reports are accessed either through the hyperlink for Backup Reports on the overview page of any of your recovery services vaults or you can also access these reports from our next service – Azure Backup Center.
Azure Backup Center
This is a unified management experience that aims to bring all Azure Backup related services under one hood. Not only can you manage and monitor your backups directly from here but there are quick access links for backup related governance features with backup policy, compliance and alerts just a single click away. This makes for a really powerful tool for an MSP who needs to manage backups across their customer base.
The initial overview dashboard when you open Backup Center gives a nice “at-a-glance” summary overview of your backups although unfortunately right now this particular report does not include the on-premises Azure Backup services: MARS, MABS and DPM.
Don’t worry though, these backup reports are still available through the Backup reports hyperlink that we covered already which is just one single click away from here.

Management and monitoring
We now have a jump site to easily manage our backup instances, policies and even the vaults themselves. Previously this required first going to the required recovery services vault which at scale could be difficult especially as some customers might have multiple recovery services vaults to check.
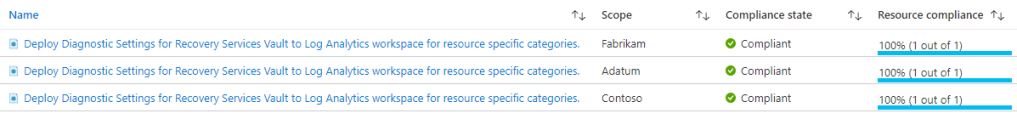
I particularly like the policy and compliance section of backup center as this allows you to configure the Azure policies relating to Azure Backup and then check their compliance status.

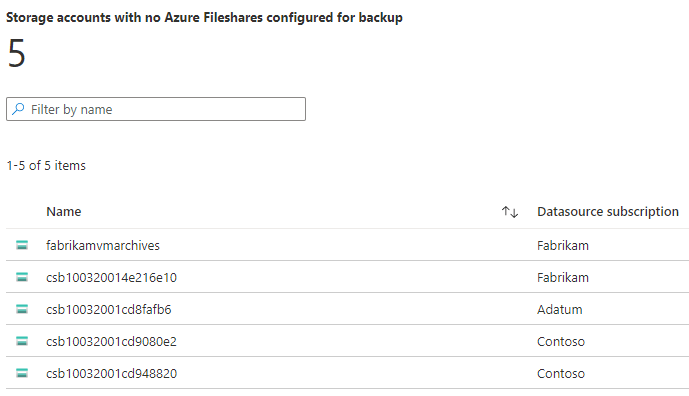
You can also quickly review any Azure resources supported by Azure Backup that are not currently being backed up.

Alerting
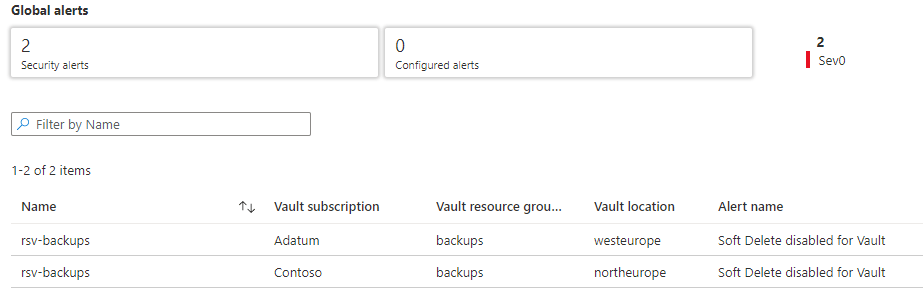
Azure Monitor works with Azure Lighthouse and this will be covered in a later post but I wanted to draw attention to a new feature which is in public preview at the time of writing. Azure backup now has some built-in monitoring support for security and job failure alerts.
This preview feature needs to be enabled per subscription initially and then you can configure alert processing rules for each customer. You should use a centralised action group that is deployed on your management tenant for your alert notifications and automated response actions.
To read more about this feature see here.
What’s next?
This concludes part 3 of this series and up next I will be talking about Azure Policy and how we can use this service to govern your customer subscriptions from a centralised location.

One thought on “MSP: The well-tempered Azure tenant – Part 3”